Disclaimer*: The articles shared under 'Your Voice' section are sent to us by contributors and we neither confirm nor deny the authenticity of any facts stated below. Parhlo will not be liable for any false, inaccurate, inappropriate or incomplete information presented on the website. Read our disclaimer.
Use of computer and internet has increased to a higher level. Every person in the world needs a computer and the internet for their daily needs. The Internet is being used by the majority of people around the world and its use is increasing at a rapid rate. The Internet is the most useful invention by humans which allows the computer user to connect to search engines, E-Commerce, chatting, payment transfer and so on.
[adinserter block=”3″]
There is always a saying that “With Good Things, Wrong Things Come as Well”. As there are many advantages of the internet, there seem to be many hidden disadvantages too which sometimes makes the internet very annoying and may result in big financial losses as well.
There are many disadvantages of the internet which put your computer systems at risk of Spyware & Malware attacks, phishing attacks, spamming, etc which might result in data corruption, data loss and even theft of confidential data which might result in big financial losses to individual and businesses as well.
Some of the most popular online cyber threats include:
1. Malicious Software:
Source: Assist Global
Malicious software is unwanted software which gets downloaded along with free softwares which users generally download from spam websites. This malicious software disturbs computer operations, leakage of confidential information or unauthorized access to private PC.
2. Denial of Service Attack:
Source: Null Byte
DOS (Denial of Service) attack is an attempt to make the landing page of any website or web application to not be reachable to its desired user and instead redirected to some other website whose sole intention is to misguide the user and initiate online fraud using the malicious software.
3. Phishing Attack:

Source: BankInfoSecurity
Phishing is an online fraud which is an attempt by the hacker which pretends to be a real and trustworthy web page on which the user has been mistakenly redirected.
4. Malware and Spyware Attack:

Source: Assist Global
Spyware and Malware are programmed softwares which are developed by a hacker to seek out confidential information from the user’s personal computer without the user knowing about it. At the present time, malware & spyware are making big losses for individuals and businesses by drawing confidential information from their computer system which includes credit card information, passwords, and other credentials.
Today we are going to list out the majors which can be adopted by computer user of they actually want to keep their computer system protected from online cyber threats.
[adinserter block=”12″]
1. Enabling Firewall:
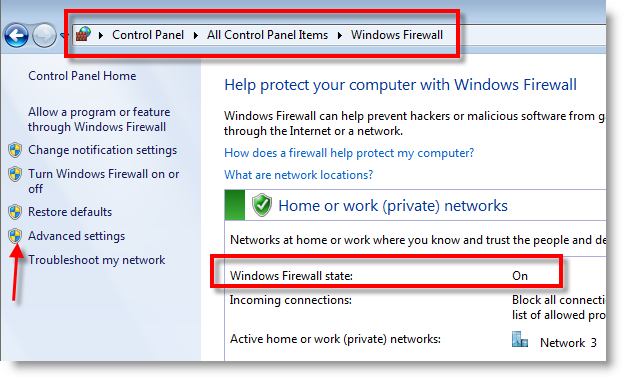
Source: Sysprobs
Firewall is the safety wall between the computer system and the internet world. Firewall is responsible for blocking spam attacks, phishing attacks, and other unauthorized access to your private computer from remote hackers with an intention to leak confidential data which might result in big financial losses.
2. Total/Internet Security Antivirus:

Source: Anti-virus4U.com
We recommend the use of total/internet security antivirus which provides extremely advanced protection from viruses, spyware, malware and other online cyber threats.
3. Password Manager:

Source: Lifehacker
We also recommend the use of password manager for the application you are installing on your computer which doesn’t allow any unauthorized user to hack the application on your computer.
4. Never Access Spam Emails:

Source: Lifehacker
Most of the cyber online threats approach your computer system from spam mail in your email. We recommend that users should not open spam emails as they contain links to spam websites which results in phishing attacks.
5. Always Install Pop-up and Ads Blocker in your Browser:

Source: Choice
Pop-up and ad locker should be installed in very computer browser which doesn’t allow malware, spyware and other attempts of phishing attacks.